Need a primer on cyber liability insurance? Our CEO Steven Legg recently had a great conversation with Cysurance CEO Kirsten Bay that was part of our live stream webinar series. The below is an excerpt from that conversation. Cysurance is a cyber insurance platform that bundles with cyber solutions to provide a deeper level of defense.
Cyber insurance industry trends
Steven Legg: Excited to have this conversation with you today. To get us started, Kirsten, what are your thoughts broadly on the overall trajectory of the cyber insurance industry in general, and where do you see it going?
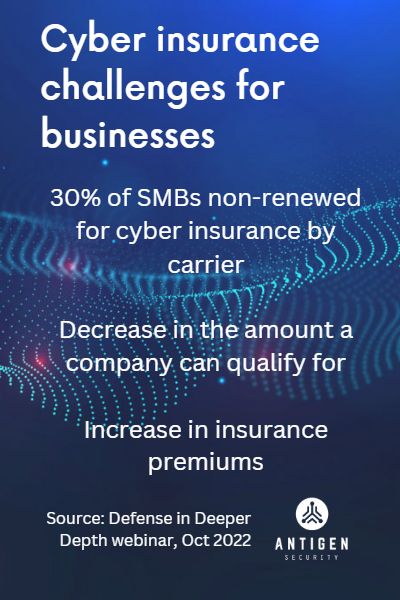
Kirsten Bay: Cyber insurance has been a much more frequent topic than is typical in the news lately. Insurance isn’t usually the most exciting topic that people are interested in hearing about, but cyber insurance certainly is, because of all of the ransomware attacks and other attacks that we’ve been experiencing that have been dramatically increasing. What we’ve seen in this last year is that almost 30% of small and medium size organizations have been non-renewed for cyber insurance. The market is also really squeezing down how much you can qualify for. Finally, we saw increases in premiums.
A lot of smaller organizations that we work with have been alarmed by the significant increases. I talked to someone at a medium size hospital. Their increase was 360% per million dollars of coverage they had. So there’s a lot of sticker shock going on. Part of it is because the insurance industry is unsure of how to protect against these cyber threats because they’re revolving forward, as opposed to a typical auto or home insurance claim where you can look backward and understand, “Where do we go from here?” Couple it with the uncertainty of where the next risks will come from in cyber, and you have what we refer to as a very hard market, both literally and metaphorically.
Legg: The bottom line is that organizations like you’re describing are experiencing this all the time. I can’t tell you how many partners and customers that we’ve seen that have traditional cyber insurance relationships through their broker that are either losing coverage mid-term because of failure to comply with either a specific vulnerability call that the carrier makes, or some other request that they’re unable to fulfill on midterm, as well as all of the risk-based circumstances you’re talking about with premiums going up.
In 2022 we’ve seen an unprecedented large amount of things like ransomware, different forms of fraud, as well as business email compromise. Those numbers are only continuing to go up, despite a lot of meaningful efforts in the industry to tamp down on that. That presents an interesting and difficult problem for insurance carriers to solve.
Bay: It absolutely does. As we look at the ransomware piece right now, if it were only so simple as making a decision to pay, not pay, negotiate, try to restore backups. Originally the predominant number of people were told: ‘If we can just recover from a backup, everything’s okay.’ Now we’re dealing with the exfiltration issue. Was it exfiltrated? If it was, what was exfiltrated? The attackers have the keys, you don’t, which means now the breach notification costs are becoming exorbitant.
That’s an area where people haven’t made the connection, where the losses aren’t necessarily even being driven by the ransomware itself. But the fact that now it’s this exfiltration concern, and now with the new rules with all of the states, such as California and Nevada, Massachusetts, etc., that are adding these new requirements, that now the costs are really almost 100x what the original loss could be. The costs have what we refer to as a very long tail, meaning that not only do we have to pay for notification, credit monitoring, but you may also have to prepare for lawsuits. This means you have to hold a potential reserve on a balance sheet on the insurance side. So the breach piece and the exfiltration concern is now becoming much more important and significant in terms of the long term risks that we all face, much beyond just the initial concern of getting that terrible screen: “You’ve been hacked.”
"Many companies ... go out of business as a result of these circumstances, just because it landed at the wrong time."
Steven Legg, Antigen Security CEO
Legg: Yes, indeed. Anybody that you would talk to who has gone through that would pay any amount of money to not have gone through it. Often you don’t hear from victim organizations. Either for disclosure reasons, which are obvious for companies that continue to operate, but there are many companies that go out of business as a result of these circumstances, just because it landed at the wrong time or hit them in a particular way that caused them to lose either customers, transactional business opportunities that were keyed up that they couldn’t execute, etc..
Bay: One of the challenges particularly for smaller organizations is the thought, “Well, I don’t really have anything anybody wants, so do I really need to make that investment?” That is one of the uphill battles both for insurance and security investments alike. Is the juice worth the squeeze?
There are more published incidents of organizations that are going out of business. I was just recently reading about a marketing firm in Arkansas that went out of business and there was a subsequent lawsuit against the carrier for not covering. They actually did have cyber insurance. But it took them over two months to try and recover. They had a particular strain of ransomware where the organization refused to negotiate.
A large medical firm in California had a similar situation. Because they refused to negotiate, the ransoming organization deleted all the patient files. So they just could not operate at all.
There is a concern with this particular situation, “Well, I had insurance and then I got a declination, and now we had to sue the insurance company, and what now? If I have it, will they even pay?” And to the point you just mentioned, that’s where this due care issue really, really comes up, because one might think that they’re compliant with their ensuring agreement, and it turns out they’re not.
Understanding expectations of the insurer
Legg: The key takeaway that I highlight to a lot of folks that I have conversations with is that it’s no longer a situation where you can just take the coolest stuff with the slickest marketing story that’s not really proven. You don’t really understand what kind of an impact it’s going to have on your cyber risk at the end of the day. That can sometimes be a recipe for disaster, depending on the circumstances. If you pick the wrong tool, if you miss something, if don’t comply with all of the requirements of the policy to the T. A lot of times in the underwriting process, the brokers are not technical people, and even some of the underwriters are not deeply technical people. They make decisions largely on a business narrative that they’re not super informed around.
This puts the policy holder in a precarious position. And that’s what creates the situations like you just described with that company that unfortunately went out of business.
I think that’s why we’re seeing overwhelming and mounting pressure on the carrier side to enforce better, more specific prescriptive requirements around what solutions need to be in place, how those things are vetted, and just to call you out, Cysurance has a really interesting solution to that in your blockchain and the technology that you use. I think the entire industry will likely go in that direction over time.
Bay: Another important thing to note is that a cyber insurance policy is actually a contract. It’s an agreement, and you are contractually obligated to do the things they require of you even if there’s a little bit of a gray area.
We will share more of this conversation in an upcoming blog post. Want to watch the entire conversation now? View it on our YouTube channel!

